SECURITY SOLUTIONS
Security Solutions
Threat intelligence
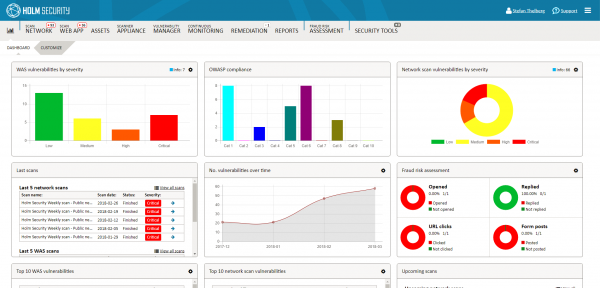
Holm Security help you get real insight Threat intelligence, also known as cyber threat intelligence (CTI), is organized, analyzed, and refined information about potential or...
View moreHolm Security VMP
Next-generation vulnerability management Holm Security is a global challenger within automated and continuous vulnerability management. Today we operate in a number of countries, mainly in...
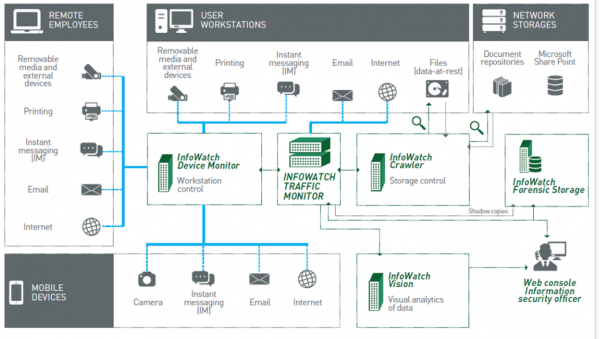
View moreInfowatch Traffic Monitor
Today, many companies defend themselves from viruses and external attacks, while the biggest threat comes from within. Even ordinary employees have access to company’s entire...
View moreInfoWatch Device Monitor
InfoWatch Device Monitor is a module for the protection of workstations, which monitors document printing and copying to removable media, and also ports and portable devices...
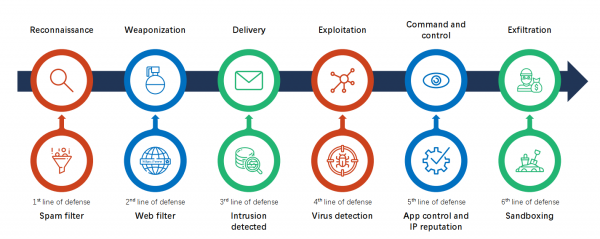
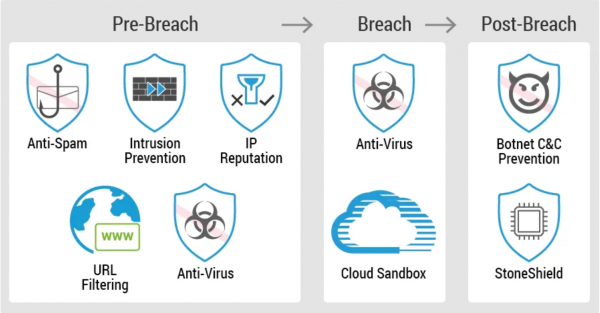
View moreHillstone Intrusion Prevention
Hillstone Intrusion Prevention Feature: • Protocol anomaly detection, rate-based detection, custom signatures, manual, automatic push or pull signature updates, integrated threat encyclopedia• IPS Actions: default,...
View moreHillstone Cloud Sanbox
Hillstone Cloud Sanbox feature • Upload malicious files to cloud sandbox for analysis• Support protocols including HTTP/HTTPS, POP3, IMAP, SMTP and FTP• Support file types...
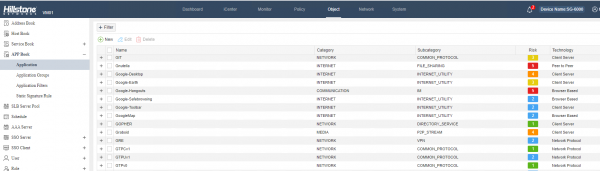
View moreHillstone Appliaction Control
Hillstone Application Control Feature: • Over 3,000 applications that can be filtered by name, category, subcategory, technology and risk• Each application contains a description, risk...
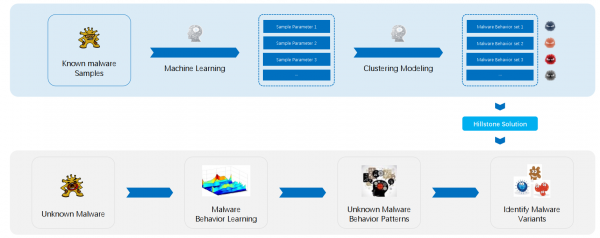
View moreHillstone Advanced Threat Detection
The Hillstone Advanced Threat Detection (ATD) Engine analyzes millions of known HTTP based malware samples with regular updates. It extracts the common characteristics of each...
View moreHillstone Anti Spam
Hillstone Anti Spam feature • Real-time spam classification and prevention • Confirmed Spam, Suspected Spam, Bulk Spam, Valid Bulk • Protection regardless of the language,...
View moreHillstone Anti Virus
Hillstone Anti Virus Manual, automatic push or pull signature updates Flow-based Antivirus: protocols include HTTP, SMTP, POP3, IMAP, FTP/SFTP Compressed file virus scanning Please view...
View moreHillstone Abnormal Behavior Detection
The Hillstone user behavior abnormal detection engine monitors and learns the normal behavior of server or host machines in the protected internal network. It extracts...
View more