Data-Driven Cyber Security
Stellar Cyber’s Starlight detects cyber breaches across your entire network, regardless of scale or complexity. When Starlight is activated, it quickly establishes a baseline behavior model for your specific environment and automatically starts identifying anomalous behaviors and breach events. Starlight’s advanced AI technology operates like an around-the-clock, autonomous virtual security analyst, ceaselessly monitoring and learning from your network. With each observation, it continues to refine its intelligence and predictive abilities. At Starlight’s core is its emphasis on pervasive data collection and its Distributed Security Intelligence™ architecture – key differentiators from other solutions.

Key Features
- Distributed, intelligent, lightweight sensors deliver pervasive coverage, eliminating all network blind spots.
- Collection, inspection, and correlation of data from many data sources including network, server, applications, events from security devices such as FW/IDS, and threat feeds.
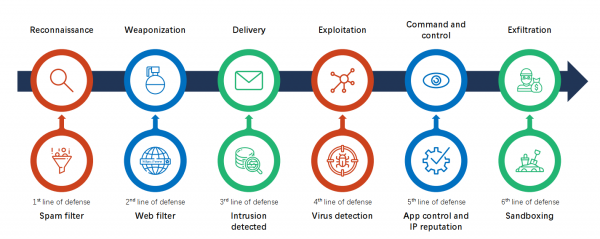
- Starlight’s Distributed Security Intelligence™ architecture supports a broad range of detections at every phase of the cyber killchain.
- With Artificial Intelligence powered analysis, alert fatigue and false alarms are effectively eliminated.
- Starlight’s big data platform supports both real-time and historic analysis and detection.
- Get a 360° view of the attack surface on critical assets.
- Flexibly and rapidly deploy pervasively in any environment – physical, virtual, containerized, in private data centers, public clouds, and/or hybrid environments.