OUR SOLUTIONS
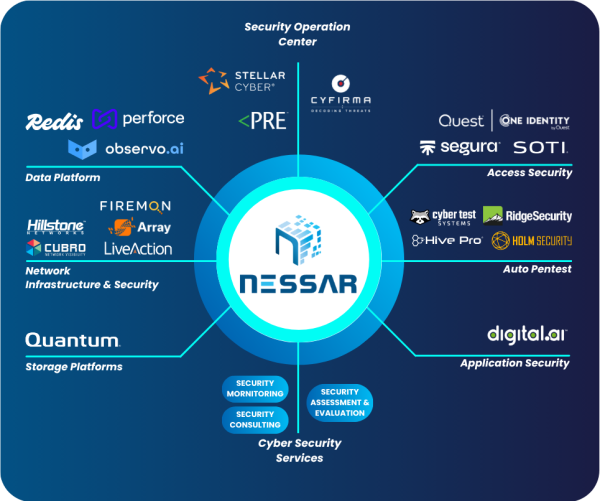
NESSAR VIETNAM – NEXT-GEN TECHNOLOGY VALUE-ADDED DISTRIBUTOR
NESSAR Viet Nam is currently the distributor of network, security and information technology products of many famous brands in the world.
Redis Open Source
Redis Open Source Redis 8 is free. Seriously. No games. Just free open source software. You read that right. It doesn’t cost anything to start...
View moreRedis Software
Redis Software Enterprise-grade Redis wherever you need it Build with the most feature-rich Redis—on premises or self managed in the cloud—and deploy how you want...
View moreRedis Cloud
Redis Cloud You know us for caching. Find out why. Build on any cloud with the highest-performing, most feature-rich Redis as a service. Start building...
View moreFireMon – Policy Manager
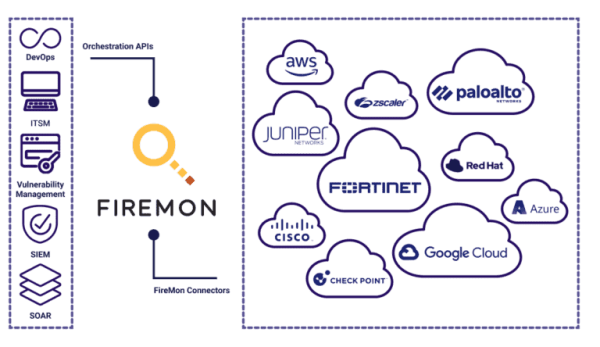
FIREMON PRODUCTS Policy Manager Automate firewall and cloud security policy management from ground to cloud. VIEW DATASHEET Unified Firewall Policy Management FireMon Policy Manager automates...
View moreFireMon – Cloud Defense
FIREMON Cloud Defense Real-time cloud security compliance, inventory, misconfiguration, and threat detection. Now with Just-In-Time IAM defense at an industry-best price. Pragmatic CSPM for Security...
View moreFireMon – Asset Manager
FIREMON PRODUCTS Asset Manager Formerly Lumeta Unmatched real-time cybersecurity asset management that enables network and security teams to discover the darkest corners of their often-obscure infrastructure....
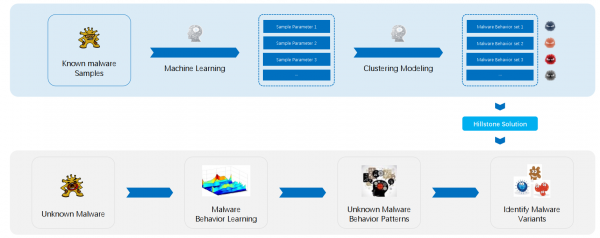
View moreStellar Cyber – Multi Layer AI
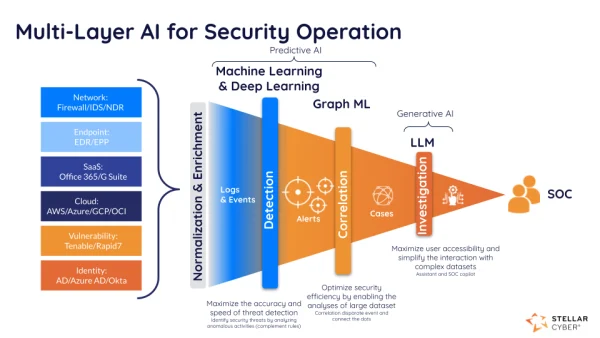
Stellar Cyber Multi-Layer AI™ The driving force behind the Stellar Cyber SecOps Platform’s ability to deliver security analyst efficiency and effectiveness gains. Take A Product...
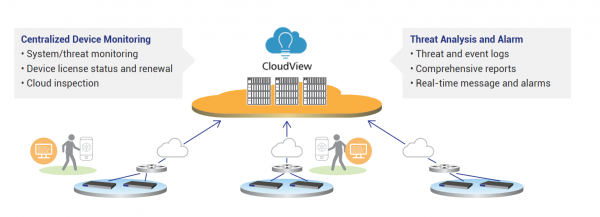
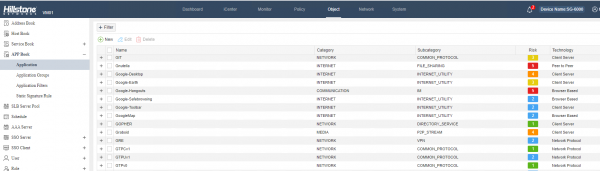
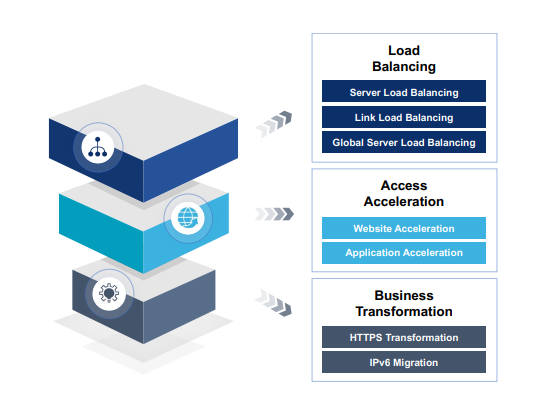
View moreHillstone – Application Delivery Controller
Protecting Critical Applications Hillstone Application Delivery Controller Solution Application Availability and Web Application Protection with Built-In Scalability Hillstone’s Application Protection products include an advanced application...
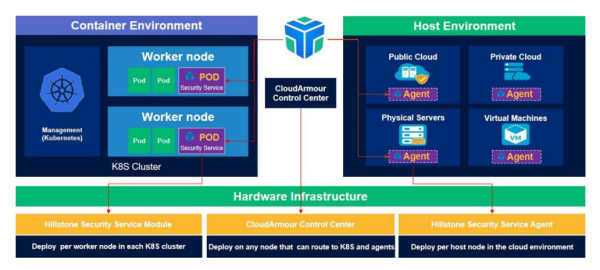
View moreHillstone – CloudArmour
Cloud Workload Protection Platform (CWPP) Hillstone CloudArmour CWPP Solution Comprehensive Cloud Workload Protection Hillstone’s CloudArmour is a CWPP solution that provides deep visibility of the...
View moreStellar Cyber – Multi Layer AI
Stellar Cyber Multi-Layer AI™ The driving force behind the Stellar Cyber SecOps Platform’s ability to deliver security analyst efficiency and effectiveness gains. Take A Product...
View moreStellar Cyber
Stellar Cyber SecOps Platform Helps You Take Control of your Security Operations Stop chasing alerts and start closing cases today. Learn more about the Stellar...
View moreStellar Cyber Photon Sensor – 10G
Photon Sensor – 10G The Photon Sensor is a network sensor that can monitor 10 LAN segments at an aggregated throughput of 1 gigabit per...
View moreStellar Cyber Photon Sensor – 1G
Photon Sensor – 1G The Photon Sensor enables organizations to gain unprecedented visibility into network security events. By solving the “Goldilocks” problem, our sensors collect...
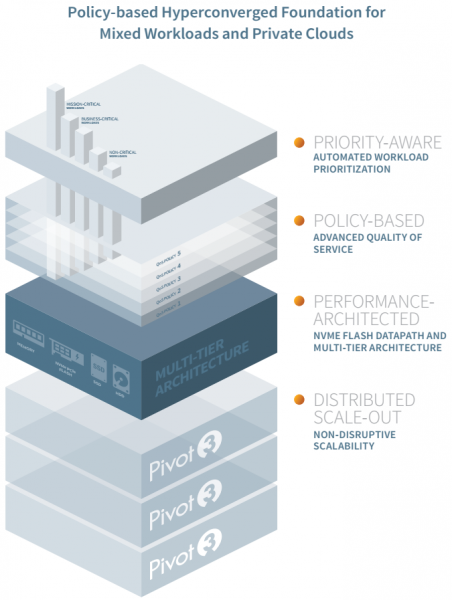
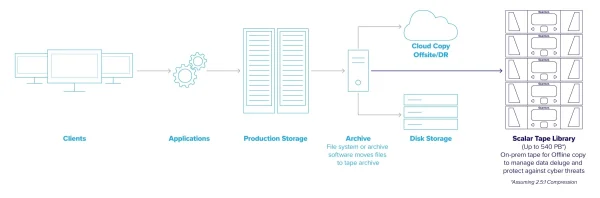
View moreQuantum – Scalar Tape Storage
Low-Cost, Reliable Long-Term Data Storage for Massive Data Growth Tape is the most cost-effective, secure storage option that requires very little power to store data...
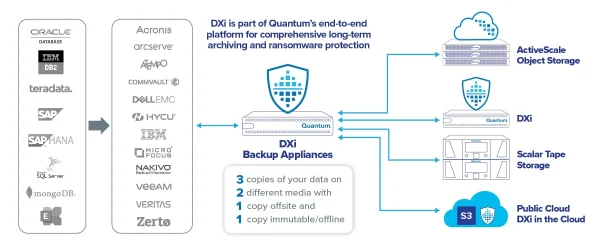
View moreQuantum – DXi Backup Appliances
Reduce Risks with Efficient Data Protection, Cyber Resilience, and Disaster Recovery Business continuity is critical to every organization, and enterprises must protect against operational risks...
View moreQuantum – ActiveScale Object Storage
Secure, Scalable S3 Object Storage for Analyzing, Managing, and Retaining Massive Data Sets With AI pipelines and other data-intensive workflows topping the list of business...
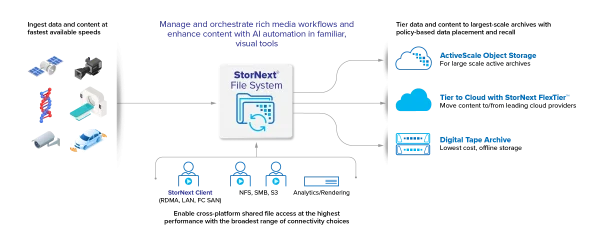
View moreQuantum – StorNext File System
Maximum Productivity and Efficiency for Your End-to-End Workflows With the demand for rich media content constantly growing, content producers need to work on fast-moving data...
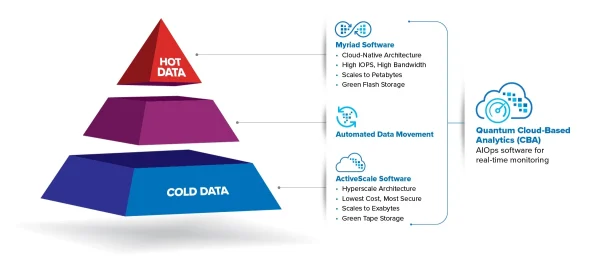
View moreQuantum – Myriad All-flash file and Object Storage
A Modern All-Flash Storage Platform Designed to Power New Workflows Modern applications like rapidly evolving data and life sciences, AI & ML, and VFX &...
View moreFireMon – Policy Manager
FIREMON PRODUCTS Policy Manager Automate firewall and cloud security policy management from ground to cloud. VIEW DATASHEET Unified Firewall Policy Management FireMon Policy Manager automates...
View moreFireMon – Cloud Defense
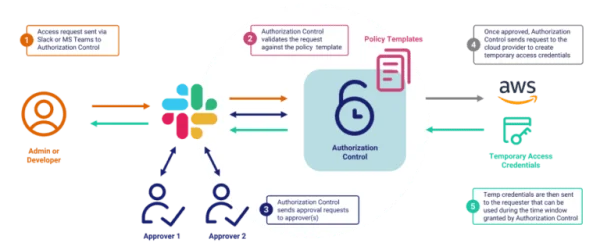
FIREMON Cloud Defense Real-time cloud security compliance, inventory, misconfiguration, and threat detection. Now with Just-In-Time IAM defense at an industry-best price. Pragmatic CSPM for Security...
View moreFireMon – Asset Manager
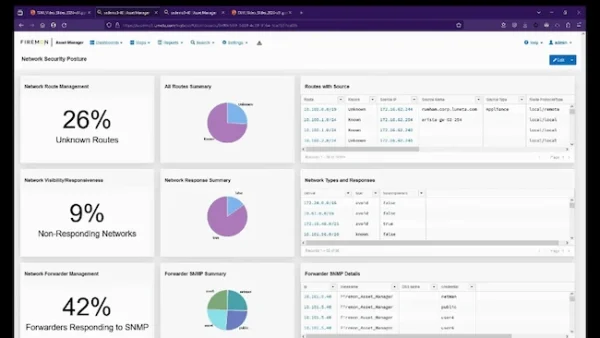
FIREMON PRODUCTS Asset Manager Formerly Lumeta Unmatched real-time cybersecurity asset management that enables network and security teams to discover the darkest corners of their often-obscure infrastructure....
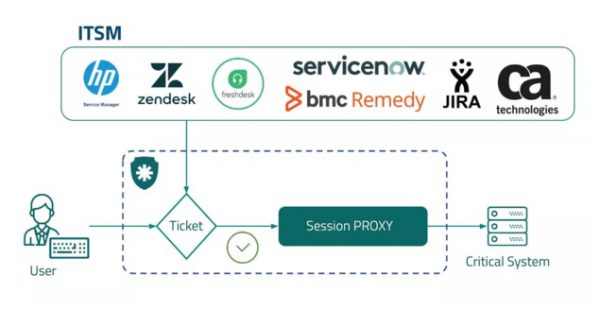
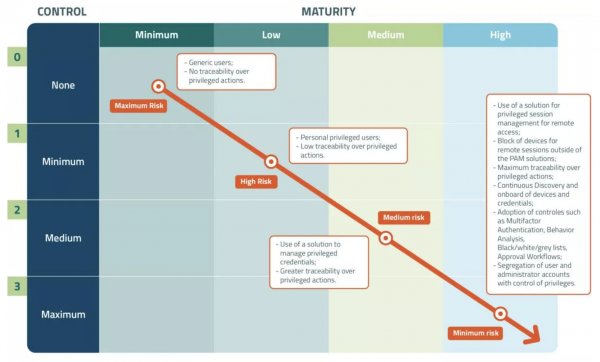
View morePAMaturity
PAMaturity Find out your PAM maturity level. We at senhasegura take Privileged Access Management (PAM) seriously. And we want to bring all of our PAM...
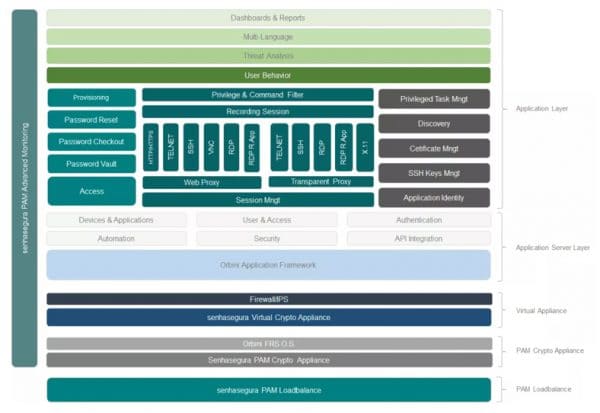
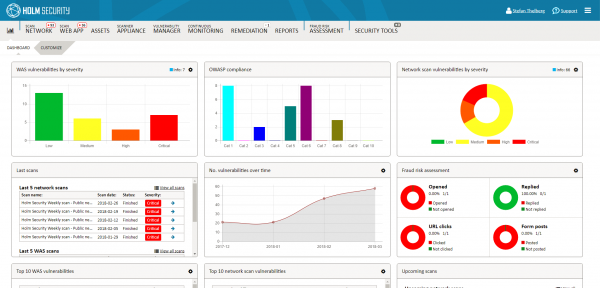
View morePAM Advanced Monitoring
PAM Advanced Monitoring Full monitoring of the senhasegura solution. What it is Monitoring of senhasegura operation aspects and its components. Benefits Operational gain in the...
View morePAM Load Balancer
PAM Load Balancer Optimal usage of senhasegura resources. What it is Integrated load balancing solution, which monitors various aspects of senhasegura Cluster and performs...
View moreLocal User Provisioning
Local User Provisioning Create and manage local users centrally. What it is Provisioning and revocation of privileged local user access on Windows, Linux and...
View moreCertificate Management
Certificate Management Automatic and centralized digital certificate management. What it is Centralized management of digital certificates lifecycle within the organization, from discovery through automatic scanning...
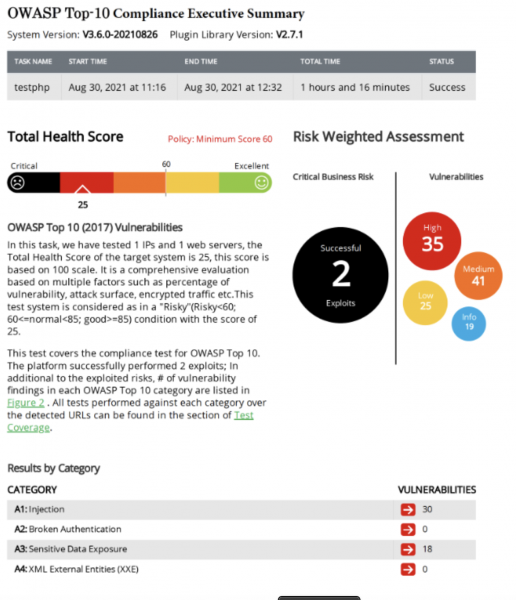
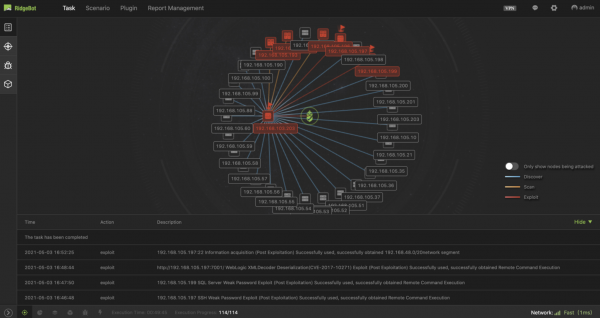
View moreOWASP Top 10 Compliance with RidgeBot 3.6
OWASP Top 10 Compliance with RidgeBot 3.6 What is OWASP Top 10? Security breaches and attacks have become so prevalent that only the very...
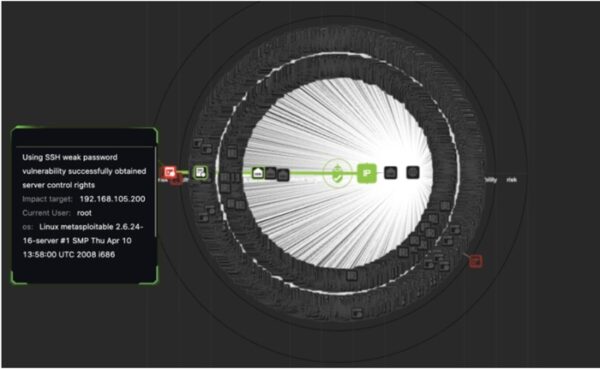
View moreRidge Security Automated Penetration Testing Solution Delivers Advanced Post-Exploitation Techniques
https://youtu.be/DzYvgEPqKCY Ridge Security Automated Penetration Testing Solution Delivers Advanced Post-Exploitation Techniques Ridge Security helps you stay on the front lines of cyber defense with...
View more10 Key RidgeBot Features
10 Key RidgeBot Features Learn how enterprise customers achieve Risk-Based Vulnerability Management using RidgeBot’s automated penetration testing technology. These 10 key RidgeBot features provide...
View moreCommercial Building
Commercial Building ACTi commercial building end-to-end solutions automate your building maintenance and security management using smart building technologies. The solutions are able to integrate surveillance,...
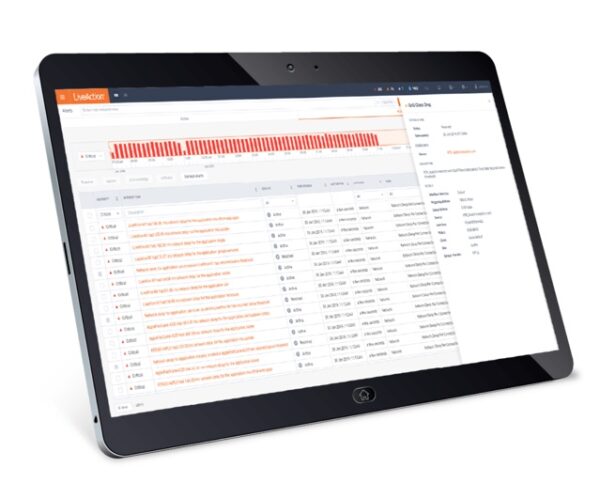
View moreACTi RAS-101
RAS-101 10-Channel Standalone Market Application Suite for Retail Application Total Traffic Performance vs Weather Total Traffic Performance vs Gender/Age Total Traffic Performance vs Weather vs...
View moreACTi RAS-100
RAS-100 100-Channel Standalone Market Application Suite for Retail Application Total Traffic Performance vs Weather Total Traffic Performance vs Gender/Age Total Traffic Performance vs Weather vs...
View moreACTi IPS-100
IPS-100 Standalone Market Application Suite Event real-time monitoring in forbidden zone to detect illegally parked vehicle, and trigger the alarm notification along with detected license...
View moreIt’s official: Redis is the #1 AI agent data storage tool
Built for devs. Trusted by devs. The 2025 Stack Overflow Developer Survey is out, and devs worldwide have spoken. They named Redis the most-used data management tool...
View moreData – The Foundation for National Digital Transformation and the Strategy for the Fourth Industrial Revolution
Data – The Foundation for National Digital Transformation and the Strategy for the Fourth Industrial Revolution Hanoi, August 1, 2025 – As part of its...
View moreDemystifying Next-Gen WAF: Meaning, Benefits & More
Demystifying Next-Gen WAF: Meaning, Benefits & More With the proliferation of threat actors on the internet, enterprises must strengthen their security backbone to mitigate modern...
View moreVietnam Cyber Law Compliance Summit 2025: Reshaping Digital Security Strategy – Solutions from Nessar
Vietnam Cyber Law Compliance Summit 2025: Reshaping Digital Security Strategy – Solutions from Nessar In the era of booming digitalization, as cyber threats grow increasingly...
View moreSix ways privilege management improves your security posture
Six ways privilege management improves your security posture Identities, computers and groups all need access to resources. But only enough to fulfill a role, and...
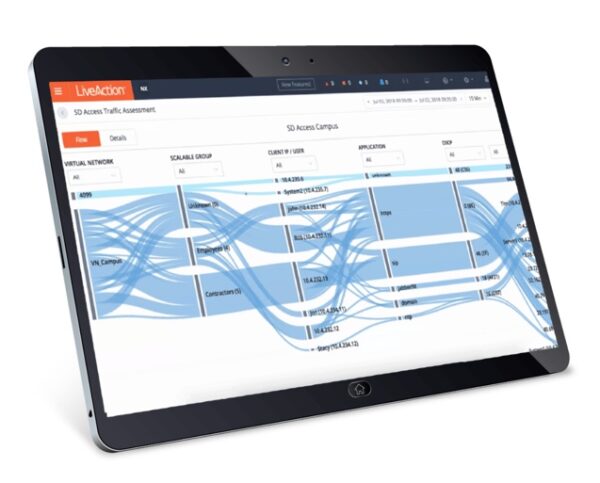
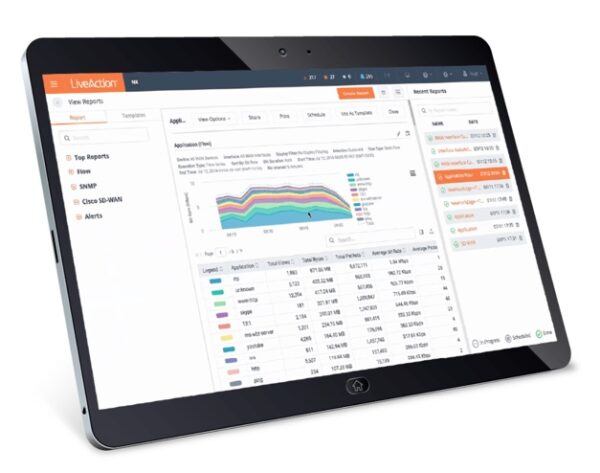
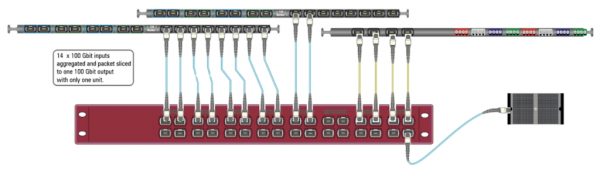
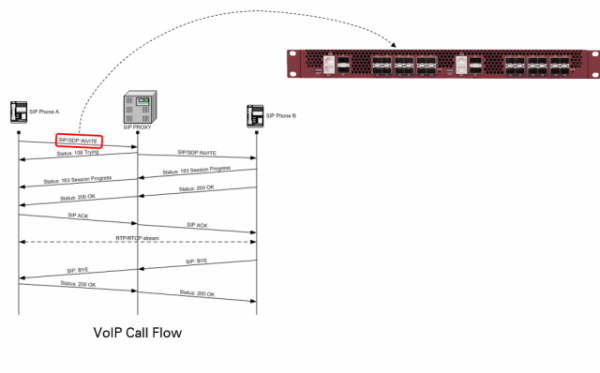
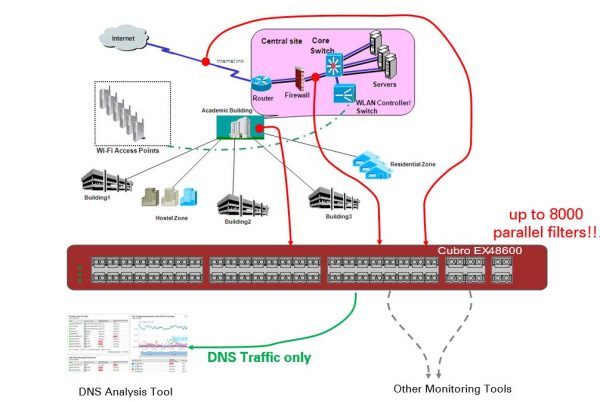
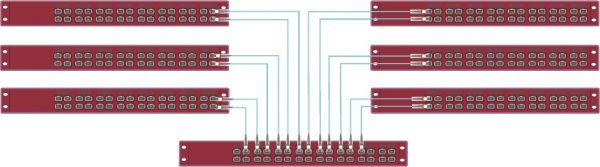
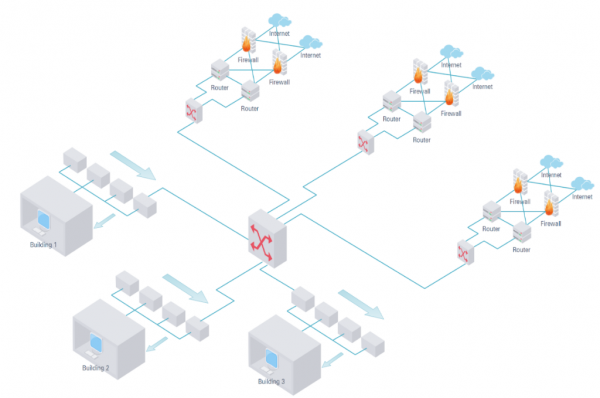
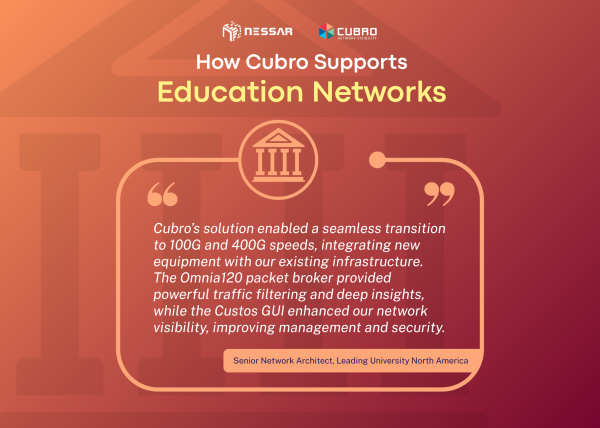
View moreEnhancing Network Visibility at a leading American University
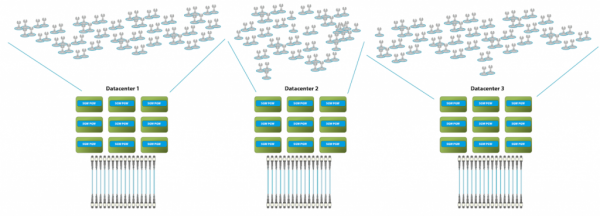
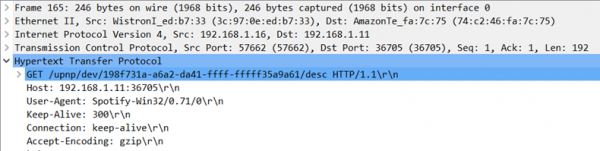
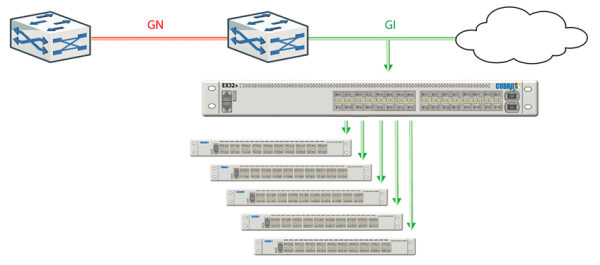
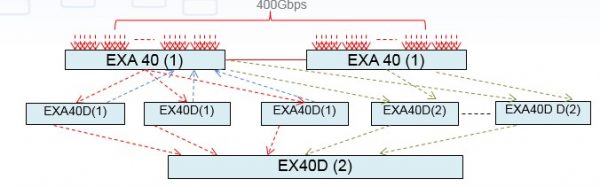
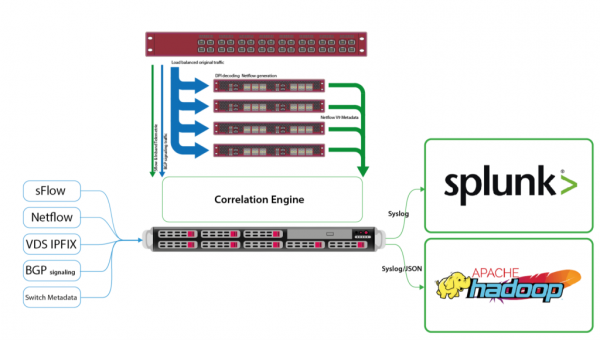
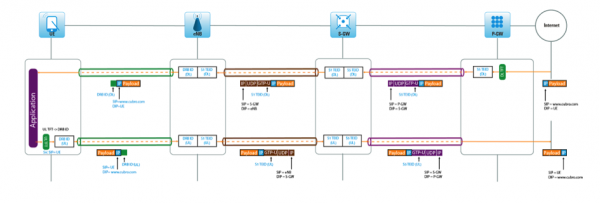
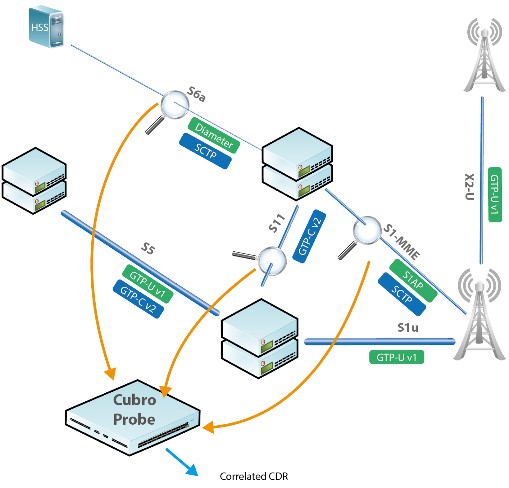
Enhancing Network Visibility at a leading American University Overview of the University The prestigious institution of higher learning ranks among the top 25 universities in...
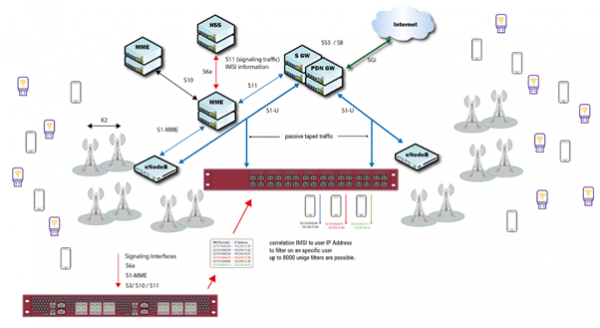
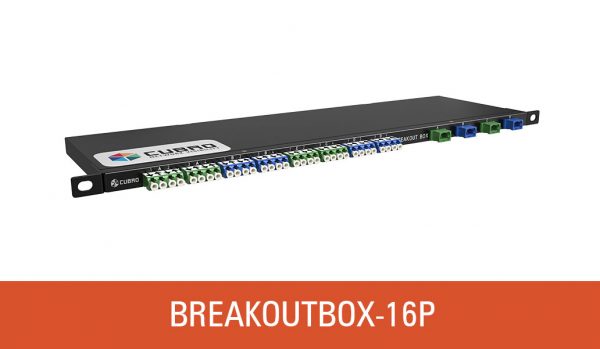
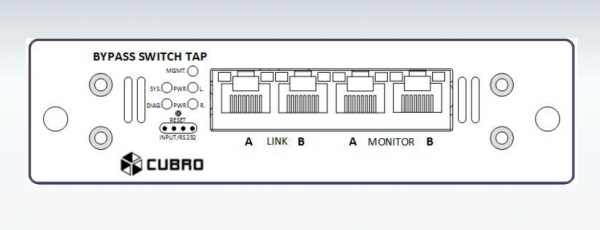
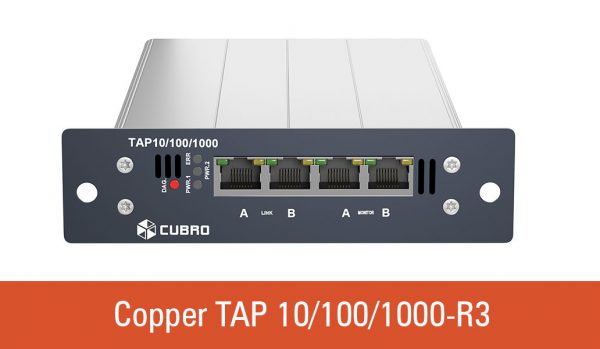
View moreEnhancing security in critical and industrial OT networks with tapping and aggregation solutions
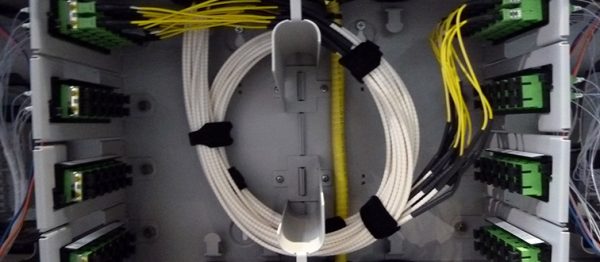
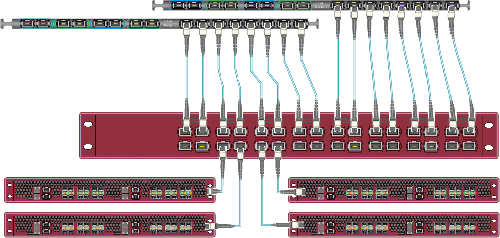
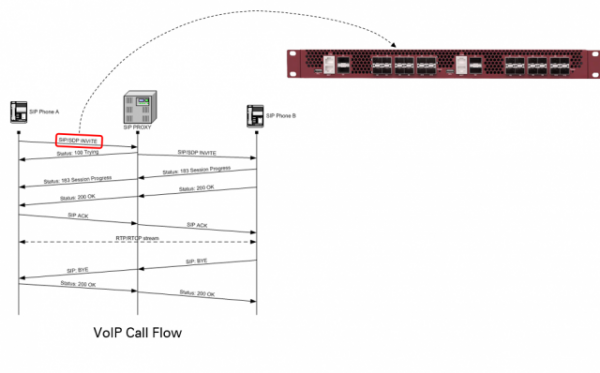
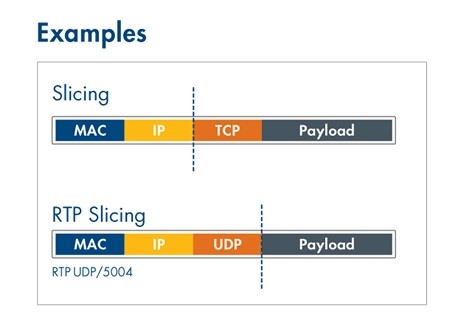
Enhancing security in critical and industrial OT networks with tapping and aggregation solutions Operational Technology (OT) encompasses the hardware and software systems vital for monitoring...
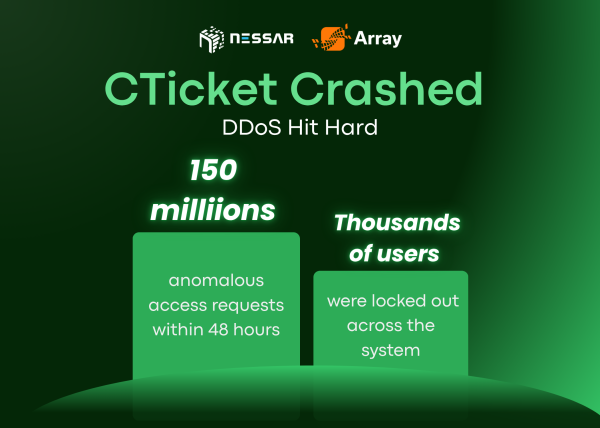
View moreWhen Clicks Turn into Chaos: Learning from the CTicket DDoS Ordeal
When Clicks Turn into Chaos: Learning from the CTicket DDoS Ordeal In today’s hyper-connected world, even a few minutes of downtime can translate into lost...
View moreIt’s official: Redis is the #1 AI agent data storage tool
Built for devs. Trusted by devs. The 2025 Stack Overflow Developer Survey is out, and devs worldwide have spoken. They named Redis the most-used data management tool...
View moreDemystifying Next-Gen WAF: Meaning, Benefits & More
Demystifying Next-Gen WAF: Meaning, Benefits & More With the proliferation of threat actors on the internet, enterprises must strengthen their security backbone to mitigate modern...
View moreVietnam Cyber Law Compliance Summit 2025: Reshaping Digital Security Strategy – Solutions from Nessar
Vietnam Cyber Law Compliance Summit 2025: Reshaping Digital Security Strategy – Solutions from Nessar In the era of booming digitalization, as cyber threats grow increasingly...
View moreSix ways privilege management improves your security posture
Six ways privilege management improves your security posture Identities, computers and groups all need access to resources. But only enough to fulfill a role, and...
View moreEnhancing Network Visibility at a leading American University
Enhancing Network Visibility at a leading American University Overview of the University The prestigious institution of higher learning ranks among the top 25 universities in...
View moreEnhancing security in critical and industrial OT networks with tapping and aggregation solutions
Enhancing security in critical and industrial OT networks with tapping and aggregation solutions Operational Technology (OT) encompasses the hardware and software systems vital for monitoring...
View moreWhen Clicks Turn into Chaos: Learning from the CTicket DDoS Ordeal
When Clicks Turn into Chaos: Learning from the CTicket DDoS Ordeal In today’s hyper-connected world, even a few minutes of downtime can translate into lost...
View moreNessar Showcases DevOps Data Platform from Perforce Delphix at Banking Roundtable on Digital Transformation
Nessar Showcases DevOps Data Platform from Perforce Delphix at Banking Roundtable on Digital Transformation On May 16, 2025, the Roundtable on “Applying AI in the...
View moreData – The Foundation for National Digital Transformation and the Strategy for the Fourth Industrial Revolution
Data – The Foundation for National Digital Transformation and the Strategy for the Fourth Industrial Revolution Hanoi, August 1, 2025 – As part of its...
View moreSOTI MobiControl 2025.1 Update: Upgrade Your Device Security & Efficiency
SOTI MobiControl 2025.1 Update: Upgrade Your Device Security & Efficiency SOTI has officially released the newest version of SOTI MobiControl 2025.1! Nessar is excited to...
View moreOpen XDR in the Financial & Banking Sector: Transforming Cybersecurity with Stellar Cyber
Securing Financial Transactions: A Major Challenge in the Financial & Banking Industry The rapid rise of digital transactions, online banking services, and fintech applications has...
View moreMaster AI Now or Risk Being Replaced: The Future of Security Operations with Stellar Cyber
In an era where Artificial Intelligence (AI) is revolutionizing every sector, including the field of cybersecurity, mastering AI is no longer optional—it’s a necessity. As...
View moreNESSAR BECOMES DISTRIBUTOR OF DELPHIX PLATFORM AND SOLUTIONS
Nessar becomes distributor of Delphix platform and solutions In the era of information explosion, the gap between the rapid growth of data technology and the...
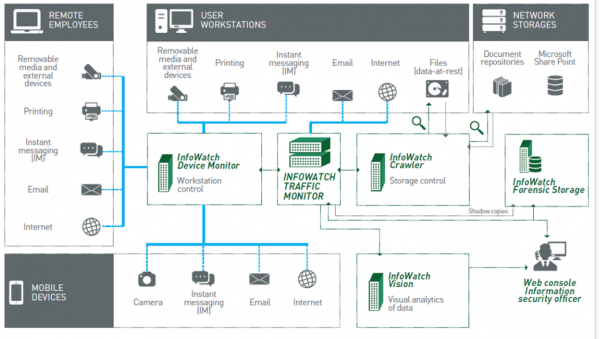
View moreDigital transformation & Automated security in network security monitoring, response, and threat intelligence
Digital transformation & Automated security in network security monitoring, response, and threat intelligence In the context of the rapidly advancing 4.0 industrial revolution, digital transformation...
View moreNessar & Quest/One Identity: Ensuring data safety more effectively than ever
Nessar & Quest/One Identity: Ensuring data safety more effectively than ever In a groundbreaking move to provide top-notch security solutions, Nessar and Quest/One Identity have...
View moreNessar Vietnam becomes the strategic distributor for Quest/One Identity in Vietnam
Nessar Vietnam becomes the strategic distributor for Quest/One Identity in Vietnam In a groundbreaking move to provide top-notch security solutions, Nessar Vietnam is pleased to...
View moreData – The Foundation for National Digital Transformation and the Strategy for the Fourth Industrial Revolution
Data – The Foundation for National Digital Transformation and the Strategy for the Fourth Industrial Revolution Hanoi, August 1, 2025 – As part of its...
View moreVietnam Cyber Law Compliance Summit 2025: Reshaping Digital Security Strategy – Solutions from Nessar
Vietnam Cyber Law Compliance Summit 2025: Reshaping Digital Security Strategy – Solutions from Nessar In the era of booming digitalization, as cyber threats grow increasingly...
View moreNessar Showcases DevOps Data Platform from Perforce Delphix at Banking Roundtable on Digital Transformation
Nessar Showcases DevOps Data Platform from Perforce Delphix at Banking Roundtable on Digital Transformation On May 16, 2025, the Roundtable on “Applying AI in the...
View moreNessar Stands in Collaboration with VNCERT/CC at the National Network Security Incident Response Conference 2023
Nessar Stands in Collaboration with VNCERT/CC at the National Network Security Incident Response Conference 2023 Quang Ninh, December 07, 2023 — Nessar proudly stands as...
View moreNessar and Quest/One Identity data security solutions make impact at The Vietnam Cyber Security Day 2023
Nessar and Quest/One Identity data security solutions make impact at The Vietnam Cyber Security Day 2023 Hanoi, November 30, 2023 – Nessar and Quest/One Identity...
View moreNessar collaborates with Quantum and Veeam to introduce data management and secure automation solutions to technology partners in Ho Chi Minh City
Nessar collaborates with Quantum and Veeam to introduce data management and secure automation solutions to technology partners in Ho Chi Minh City Following the success...
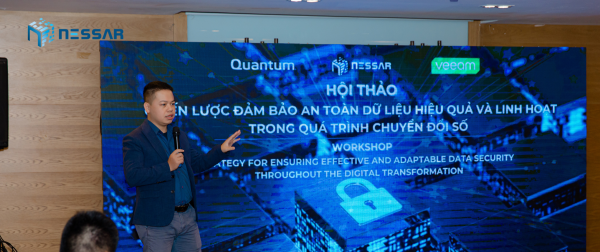
View moreNessar collaborates with Quantum and Veeam to organize the workshop “Strategy for ensuring effective and adaptable data security throughout the digital transformation”
Nessar collaborates with Quantum and Veeam to organize the workshop “Strategy for ensuring effective and adaptable data security throughout the digital transformation” On November 21,...
View moreDigital transformation & Automated security in network security monitoring, response, and threat intelligence
Digital transformation & Automated security in network security monitoring, response, and threat intelligence In the context of the rapidly advancing 4.0 industrial revolution, digital transformation...
View moreIt’s official: Redis is the #1 AI agent data storage tool
Built for devs. Trusted by devs. The 2025 Stack Overflow Developer Survey is out, and devs worldwide have spoken. They named Redis the most-used data management tool...
View moreData – The Foundation for National Digital Transformation and the Strategy for the Fourth Industrial Revolution
Data – The Foundation for National Digital Transformation and the Strategy for the Fourth Industrial Revolution Hanoi, August 1, 2025 – As part of its...
View moreDemystifying Next-Gen WAF: Meaning, Benefits & More
Demystifying Next-Gen WAF: Meaning, Benefits & More With the proliferation of threat actors on the internet, enterprises must strengthen their security backbone to mitigate modern...
View moreEnhancing Network Visibility at a leading American University
Enhancing Network Visibility at a leading American University Overview of the University The prestigious institution of higher learning ranks among the top 25 universities in...
View moreWhy Stellar Cyber’s Open Cybersecurity Alliance Is a Game-Changer for MSSPs and Enterprises Alike
Why Stellar Cyber’s Open Cybersecurity Alliance Is a Game-Changer for MSSPs and Enterprises Alike The cybersecurity world has long struggled with a fundamental challenge: how...
View moreStellar Cyber unveils Human-Augmented Autonomous SOC Powered by Agentic AI
Stellar Cyber unveils Human-Augmented Autonomous SOC Powered by Agentic AI Organizations today are navigating an environment where threats are not only more frequent, but also...
View moreStellar Cyber Recognized as a Leader and Outperformer in GigaOm Radar for XDR v4
Stellar Cyber Recognized as a Leader and Outperformer in GigaOm Radar for XDR v4 April 2025 – Stellar Cyber, the leading provider of Open XDR...
View moreThe Urgency of Data Protection: Why It Matters More Than Ever
The Urgency of Data Protection: Why It Matters More Than Ever The Growing Data Explosion In today’s digital world, data is expanding at an unprecedented...
View moreFREQUENTLY ASKED QUESTIONS
Synthesize the most frequently asked questions for customers as well as consultantsOur moral compass
Customer satisfaction is our top priority.
The company’s leaders pay great attention to customer care. For that reason, all NESSAR employees not only improve their expertise during their work, but also learn how to communicate and take care of customers in the most professional way.